
As July and August signal the return to school for millions of children, this year brings unique challenges. With the pandemic shifting many to remote learning, parents worldwide are prioritizing online safety.
By August 18, Education Week reported that 20 of the 25 largest U.S. school districts opted for fully remote instruction, impacting over 4.3 million students. Districts like Los Angeles Unified, San Diego Unified, Nashville, and Palm Beach County led the way. Across the U.S.'s 13,000+ public school systems, this trend prioritizes health while raising critical questions: How can we keep kids safe online? How do we guard against hackers and cyberbullying? Are remote learning tools secure?
At Check Point Software Technologies, our researchers address these concerns head-on, drawing from years of threat intelligence and hands-on vulnerability assessments.
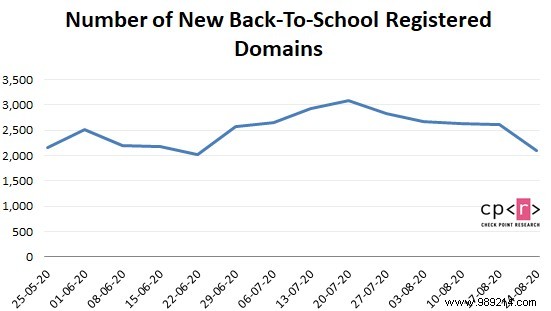
Check Point Research analyzed three months of domain registration data, revealing heightened cybercriminal activity:
Figure 1: New back-to-school domains registered weekly over the last three months.
In early 2020, Check Point experts audited popular learning management systems, including WordPress plugins like LearnPress, LearnDash, and LifterLMS. We uncovered critical flaws exploitable by hackers—now patched—but underscoring ongoing risks in remote education tech.
Children face tangible dangers:
– Zoomombing: Uninvited intruders disrupt Zoom calls with slurs, profanity, or offensive images. A San Diego school incident featured a masked intruder making lewd gestures, potentially traumatizing students.
– Cyberbullying: Harmful online content targeting peers. The Cyberbullying Research Center notes 37% of 12-17-year-olds affected, 30% repeatedly—impacting mental health.
– Ransomware: In 2019, over 1,000 U.S. schools hit by malware locking systems until ransom paid, often via deceptive emails.
– Phishing: Fraudulent messages tricking users into sharing sensitive data like passwords.
Our cybersecurity experts recommend these proven strategies:
Source: Check Point Software Technologies Ltd.